Algemene Voorwaarden
Download onze Algemene Voorwaarden
Laatste update: december 2023.
Hierna vindt u de algemene voorwaarden van Smartlockr B.V. H.J.E Wenckebachweg 123, 1096 AM Amsterdam Kamer van Koophandel nummer 61781614. ("wij", "ons" of "onze"). Deze algemene voorwaarden zijn van toepassing op onze aanbiedingen en maken deel uit van iedere overeenkomst die wij met u sluiten. "U" is de (potentiële) klant aan wie wij een aanbieding hebben gestuurd of met wie wij een overeenkomst hebben gesloten.
1. Definities
De begrippen die in deze AV of elders in de Overeenkomst worden gebruikt en die met een hoofdletter beginnen, hebben de betekenis die er hieronder aan wordt gegeven.
- 1.1 “AV”: deze algemene voorwaarden inclusief Annex 1 en Annex 2.
1.2 "Clouddienst": onze levering op afstand van de Functionaliteit aan u via het Internet, inclusief de bijbehorende Ondersteuning en Documentatie.
1.3 "Diensten": alle diensten die door ons aan u worden geleverd of zullen worden geleverd onder de Overeenkomst, inclusief Ondersteuning en Documentatie.
1.4 "Documentatie": de documentatie over de Clouddienst die wij via de gebruikersinterface van de Clouddienst aan u hebben verstrekt.
1.5 "Functionaliteit": de mogelijkheid om e-mail met bijbehorende (grote) gegevensbestanden veilig te verzenden, rechtstreeks vanuit Microsoft Outlook. Daarnaast kunnen Gebruikers gegevensbestanden ontvangen via een uploadverzoek dat via Microsoft Outlook wordt ingediend door middel van een daarvoor bestemde uploadpagina. De beheerderstool stelt u in staat het gebruik van de Clouddienst of de Software te monitoren en daarmee controle uit te oefenen over uw bedrijfsmiddelen. Monitoring vindt plaats door middel van logging, filters op bestandstype en e-mailadressen en de beschikbaarheid van verzonden gegevens voor de ontvanger. Een volledig overzicht van de Functionaliteit is te vinden in de Documentatie.
1.6 "Geaccepteerde Voorstel": ons voorstel voor de levering van een of meer Diensten dat u schriftelijk of elektronisch hebt geaccepteerd.
1.7 "Gebruiker": iemand die door u is aangewezen om de Functionaliteit of de Software te gebruiken.
1.8 "Incident": dit is de situatie waarbij de Clouddienst of de Software niet werkt in overeenstemming met de Documentatie.
1.9 "Ingangsdatum": de ingangsdatum van de Looptijd zoals aangegeven op het Geaccepteerde Voorstel.
1.10 "Intellectuele eigendomsrechten": alle intellectuele eigendomsrechten waar ook ter wereld, geregistreerd of niet-geregistreerd, met inbegrip van elke aanvraag of recht van aanvraag voor dergelijke rechten (deze "intellectuele eigendomsrechten" omvatten onder meer auteursrechten en naburige rechten, databankrechten, handelsgeheimen, vertrouwelijke informatie, knowhow, handelsnamen, handelsmerken, dienstmerken, rechten om producten te laten passeren, oneerlijke concurrentierechten, octrooien en rechten op tekeningen of modellen).
1.11 "Kantooruren": uren op Werkdagen tussen 08.30 en 17.30 uur (Nederlandse tijd).
1.12 "Looptijd": de termijn van de Overeenkomst. Dit is de termijn waarvoor u van ons een licentie heeft gekregen om de Clouddienst of de Software te gebruiken. De toepasselijke termijn staat in het Geaccepteerde Voorstel.
1.13 "Ondersteuning": wanneer wij u tijdens Kantooruren informatie en advies geven over het gebruik van de Functionaliteit of de Software, inclusief het bieden van hulp bij het onderzoeken van oorzaken, inclusief Defecten, die het ongestoord gebruik van de Clouddienst of de Software verhinderen.
1.14 "Opleiding": wanneer wij Gebruikers vertrouwd maken met de Functionaliteit en hen opleiden in het gebruik ervan.
1.15 "Overeenkomst": de overeenkomst die wij met u hebben gesloten, welke is vastgelegd in het Geaccepteerde Voorstel plus deze AV inclusief Annex 1 (AUP) en Annex 2 (Verwerkersovereenkomst).
1.16 "Platform": het Smartlockr Data Protection Platform; het IT-platform dat wij gebruiken om Gebruikers toegang te geven tot de Functionaliteit. Het Platform bestaat uit de combinatie van het hostingplatform, onze SMTP-server, de Software en de integraties met de diensten van onze toeleveranciers.
1.17 “Plugin”: de Outlook plugin die wij aan u ter beschikking stellen om gebruik te kunnen maken van de Functionaliteit, zoals nader beschreven in artikel 7.
1.18 "Responstijd: dit is de tijd die wij nodig hebben om u een eerste reactie te geven op uw melding van een incident. Deze tijd begint te lopen vanaf de datum van onze ontvangst van uw melding, ervan uitgaande dat u deze correct aan ons hebt doorgegeven.
1.19 "Software": de software die is geïnstalleerd op het Platform.
1.20 "Toegestaan doel": het op een veilige manier verzenden van digitale bestanden via Microsoft Outlook.
1.21 "Toepasselijk recht inzake gegevensbescherming" betekent alle wet- en regelgeving en sectorale aanbevelingen met regels voor gegevensbescherming en privacy die van toepassing zijn op de verwerking van Persoonsgegevens in het kader van de Overeenkomst (bijv. de Algemene Verordening Gegevensbescherming 2016/679/EG), met inbegrip van maar niet beperkt tot beveiligingsvereisten.
1.22 “Update”: betekent een gedeeltelijke vernieuwing van het Platform aangeduid met een aanpassing van het bestaande versienummer, bijvoorbeeld 5.x.
1.23 “Upgrade”: een volledige vernieuwing van het Platform aangeduid met een nieuw versie nummer, bijvoorbeeld versie 5.
1.24 "Website” https://www.smartlockr.io en andere bijbehorende sub-domeinen, indien van toepassing.
1.25 "Werkdagen”: Maandag tot en met vrijdag, met uitzondering van de nationale feestdagen in Nederland, met dien verstande dat de vijfde mei éénmaal in de vijf jaar een nationale feestdag is.
2. Toepasselijkheid en interpretatie
- 2.1 De AV zijn van toepassing op en maken deel uit van elke handeling met betrekking tot de voorbereiding, totstandkoming of uitvoering van de Overeenkomst. Elke Overeenkomst komt tot stand door dat de volgende stappen worden doorlopen: (i) u accepteert ons voorstel en (ii) wij bevestigen per e-mail aan u dat wij uw acceptatie hebben ontvangen. U accepteert ons voorstel door het online elektronisch te ondertekenen of offline te voorzien van een handtekening en dan aan ons te retourneren. In het Geaccepteerde Voorstel staan de Diensten beschreven die u van ons afneemt en de bijbehorende prijzen en tarieven.
- 2.2 Afwijkingen op het Geaccepteerde Voorstel en de AV zijn alleen geldig als deze schriftelijk zijn overeengekomen.
2.3 Bij tegenstrijdigheden tussen de verschillende documenten geldt de volgende rangorde:- a. Annex 2 (Verwerkersovereenkomst) bij de AV;
b. Het Geaccepteerde Voorstel; - c. De AV met uitzondering van Annex 2.
- a. Annex 2 (Verwerkersovereenkomst) bij de AV;
- 2.4 Wij kunnen deze AV eenzijdig wijzigen. Als wij dit doen, zullen wij u ten minste drie (3) maanden voor de verlengingsdatum van de Overeenkomst per e-mail op de hoogte stellen van ons voornemen. Als u gebruik blijft maken van de Diensten nadat u onze kennisgeving heeft ontvangen, wordt u geacht hierdoor akkoord te gaan met de gewijzigde AV. Accepteert u de wijziging niet, dan is uw enige recht om kosteloos de Overeenkomst beëindigen tegen de verlengingsdatum.
3. Voorstel en acceptatie
- 3.1 Ons voorstel is vrijblijvend, tenzij het een uitdrukkelijke termijn voor aanvaarding bevat.
3.2 U moet ons tijdig alle (technische) informatie, besluiten en inlichtingen verschaffen die wij redelijkerwijs nodig hebben voor onze uitvoering van de Overeenkomst. Wij zijn niet verantwoordelijk als u ons onjuiste of onvolledige informatie verstrekt. Wij mogen onze uitvoering van de Overeenkomst opschorten wanneer u ons niet tijdig van juiste en volledige informatie voorziet.
4. Samenwerking
- 4.1 Wij zullen redelijke commerciële inspanningen verrichten om overeengekomen (leverings)data en termijnen na te komen. Alle data en termijnen zijn steeds indicatief, tenzij uitdrukkelijk wordt vermeld dat het om fatale data of termijnen gaat.
- 4.2 Wij zullen de Cloud Dienst aan u leveren of de Software bij u installeren binnen een week na ontvangst van de ondertekende Overeenkomst, tenzij wij schriftelijk een andere termijn met u zijn overeengekomen.
- 4.3 De Cloud Dienst zal door ons geleverd worden op een zogenaamde best effort-basis: Wij zullen de Cloud Dienst zo goed mogelijk leveren maar accepteren hiervoor geen resultaatsverbintenis.
- 4.4 Wij mogen derden in te schakelen om de Overeenkomst uit te voeren.
5. Het Platform
- 5.1 Wij zullen u toegang verlenen tot het Platform door binnen 3 (drie) Werkdagen na de Ingangsdatum u een licentiesleutel te verstrekken. De licentiesleutel zal de Plug-in activeren. Na de installatie van de Plug-in krijgt u toegang tot de Functionaliteit voor het overeengekomen aantal gelicentieerde Gebruikers.
5.2 Binnen de beperkingen zoals beschreven in artikel 5.3, verlenen wij hierbij aan u een niet-exclusieve licentie om het Platform te gebruiken voor het Toegestane Doel via de Plug-in of via een directe online toegang tot het Platform. Uw licentie is geldig voor de Looptijd en u bent verplicht het Platform te gebruiken in overeenstemming met de Documentatie.
5.3 De licentie die wij u verlenen is onderworpen aan de volgende beperkingen:- a. Het Platform mag niet worden gebruikt door meer dan het aantal gelicentieerde Gebruikers vermeld in het Geaccepteerde Voorstel, met dien verstande dat u bij ons een verzoek kunt indienen om Gebruikers toe te voegen of te verwijderen;
- b. Het Platform mag alleen worden gebruikt door uw werknemers, uitzendkrachten en ander tijdelijk personeel en onderaannemers; en
c. U moet altijd voldoen aan het Beleid inzake Aanvaardbaar Gebruik zoals uiteengezet in Annex 1 ("AUP"), en moet ervoor zorgen dat alle Gebruikers zich aan de AUP houden.
- 5.4 Alles dat wordt uitgevoerd via de Plug-in met uw licentiesleutel of direct online via het Platform met uw toegangsgegevens, is voor uw verantwoordelijkheid en risico. Als u weet of vermoedt dat uw licentiesleutel niet langer uitsluitend door u wordt gebruikt moet u ons hiervan onmiddellijk op de hoogte te stellen.
5.5 U hebt geen recht op toegang tot de objectcode of broncode van het Platform, noch tijdens noch na de Looptijd.
5.6 Alle Intellectuele Eigendomsrechten in het Platform zijn ons exclusief eigendom.
5.7 U mag het Platform niet gebruiken op een manier die schade veroorzaakt of kan veroorzaken aan het Platform of afbreuk doet aan de beschikbaarheid of toegankelijkheid van het Platform, of een van de gebieden van, of diensten op, het Platform. In het bijzonder zult de Cloud Dienst niet gebruiken op een manier die een systeem- en netwerkbelasting op het Platform veroorzaakt die hoger is dan die van onze gemiddelde klant.
5.8 U mag het Platform niet gebruiken:- a. Op een wijze die onwettig, frauduleus of schadelijk is; of
b. In verband met een onwettig, frauduleus of schadelijk doel of activiteit.
- a. Op een wijze die onwettig, frauduleus of schadelijk is; of
- 5.9 Wij bieden een beschikbaarheid voor het Platform van 99,95%. Het Platform is beschikbaar als de Cloud Dienst toegankelijk is voor Gebruikers vanaf het Internet.
- De werkelijke beschikbaarheid wordt door ons per kalenderkwartaal berekend volgens de volgende formule. AST staat voor Agreed Service Time, de periode waarin het Platform geacht wordt beschikbaar te zijn en DT staat voor downtime:
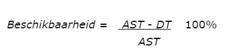
Ons berekende beschikbaarheidspercentage over een kalenderkwartaal wordt u op verzoek aan u gerapporteerd. Als de werkelijke beschikbaarheid in twee opeenvolgende kalenderkwartalen daalt tot onder 99,95%, heeft u het recht de Overeenkomst zonder kosten te beëindigen. U heeft geen andere rechten in verband met het niet halen van het beschikbaarheidspercentage.
6. Platform updates en upgrades
6.1 Wij introduceren gedurende de Looptijd Updates en/of Upgrades van het Platform. Een Update of een Upgrade kan bijvoorbeeld inhouden dat de Software is aangepast, nieuwe filter technieken zijn geïntroduceerd of processen zijn aangepast. Als er een Update of Upgrade door ons wordt geïntroduceerd, heeft dit een eenzijdige aanpassing van de door u afgenomen Diensten tot gevolg. Een overzicht van de aanpassingen van de Diensten publiceren wij vooraf via de Website. Een Update of Upgrade biedt altijd een Functionaliteit die materieel vergelijkbaar is met of ruimer is dan de Functionaliteit van de voorlaatste versie van het Platform.
6.2 Een Upgrade van het Platform kan een aanpassing van de technische implementatie van de Diensten in uw omgeving noodzakelijk maken. Als dit zo is, zullen wij u vooraf per e-mail van de noodzakelijke implementatie aanpassingen op de hoogte stellen. U dient de aanpassingen zelf en op eigen kosten te realiseren. Op uw verzoek kunnen wij u hierbij ondersteunen. Voor onze ondersteuning mogen wij de gemaakte uren bij u in rekening brengen tegen onze dan geldende tarieven.
6.3 Indien artikel 6.2 van toepassing is en u nalaat om uiterlijk binnen 3 (drie) maanden na onze notificatie de noodzakelijke implementatie aanpassingen door te voeren, hebben wij het recht om eenzijdig de Overeenkomst te beëindigen zonder dat wij in verband met die beëindiging aan u een vergoeding moeten betalen voor eventueel door u geleden schade of gemaakte kosten. Als u niet bereid bent om de aanpassingen te realiseren heeft u het recht om kosteloos de Overeenkomst te beëindigen. U dient uw beëindiging uiterlijk 1 (één) maand na onze notificatie aan ons per e-mail te melden.
7. Platform Integratie
7.1 Om gebruik te laten maken van de Functionaliteit is een integratie van uw e-mail omgeving met het Platform nodig. Integratie kan op e-mail-client niveau (de Plug-in) en op e-mailserver niveau (SMTP-relay). Welke (combinatie van) integratie middelen voor u van toepassing zijn, hangt af van de implementatie afspraken die wij met u hebben gemaakt. De volgende leden van dit artikel zijn van toepassing op uw gebruik van de betreffende integratie middelen gebruik maakt.
7.2 Nadat wij u de licentiesleutel zoals beschreven in artikel 5.1 hebben verstrekt, zullen wij u doorverwijzen naar een online downloadlocatie voor de Plug-in. U bent verantwoordelijk voor het vervolgens downloaden van de Plug-in.
7.3 Uw gebruik van de Plug-in is onderworpen aan de volgende licentievoorwaarden:
-
- a. U mag de Plug-in alleen voor uw eigen zakelijke doeleinden gebruiken;
- b. U mag een aantal Plug-ins downloaden, installeren en gebruiken dat maximaal gelijk is aan het aantal gelicentieerde Gebruikers;
- c. U mag niet:
-
- (i) De Plug-in of enig deel daarvan kopiëren of reproduceren, anders dan in overeenstemming met de in dit artikel 7 verleende licentie;
(ii) De Plug-in of enig deel van de Plug-in verkopen, doorverkopen, verhuren, leasen, uitlenen, leveren, distribueren, of opnieuw openbaar maken;
(iii) De Plug-in of enig deel van de Plug-in wijzigen, aanpassen, vertalen of bewerken, of daarvan afgeleide werken te maken;
(iv) De Plug-in of enig deel van de Plug-in reverse-engineeren, decompileren of disassembleren (behalve zoals voorgeschreven door de toepasselijke wetgeving);
(v) De Plug-in anders gebruiken dan in overeenstemming met de Documentatie; of
(vi) De op de Plug-in toegepaste technische maatregelen ter voorkoming van onbevoegd gebruik omzeilen of verwijderen, of trachten deze te omzeilen of te verwijderen.
- (i) De Plug-in of enig deel daarvan kopiëren of reproduceren, anders dan in overeenstemming met de in dit artikel 7 verleende licentie;
7.4 Alle Intellectuele Eigendomsrechten in de Plug-in zijn ons exclusieve eigendom.
7.5 U bent verantwoordelijk voor de beveiliging van uw kopieën van de Plug-in en zult alles doen wat redelijkerwijs mogelijk is om ervoor te zorgen dat alleen bevoegde Gebruikers deze kopieën kunnen inzien en gebruiken.
7.6 Bij SMTP-relay stellen wij samen met u uw SMTP-server zo in dat deze alle uitgaande e-mail via een TLS (Transport Layer Security) verbinding verstuurd naar een SMTP-server op het Platform. Op basis van een ingesteld content beleid wordt dan de gewenste beveiliging toegepast en wordt de e-mail verzonden naar de ontvanger. Het content beleid kan handmatig zijn op basis van opgegeven sleutelwoorden of automatisch door het toepassen van een door ons ontwikkeld algoritme. Bij een handmatig beleid bent u verantwoordelijk voor het vooraf aan ons opgeven van een complete en correcte lijst met sleutelwoorden. Uw accepteert dat toegepast content beleid nooit alomvattend is. Wij garanderen niet dat al uw verzonden e-mail op het door u gewenste niveau zal zijn beveiligd.
7.7 U accepteert dat wij bij gebruik van SMTP-relay e-mail doorzenden met gebruikmaking van een externe e-mail bezorgdienst. Dit houdt onder meer in dat de e-mail headers de IP-adressen van de servers van de externe e-mail bezorgdienst kunnen bevatten. Wij garanderen niet dat door ons doorgestuurde e-mail altijd aankomt of nooit wordt voorzien van een spam label.
8. Ondersteuning en onderhoud
8.1 Als onderdeel van onze Ondersteuning zullen wij u in staat stellen contact met ons op te nemen via e-mail en telefoon voor vragen met betrekking tot uw gebruik van het Platform en de Software of voor het melden van Incidenten aan ons. Onze E-mail en telefonische contactgegevens voor Ondersteuning staan op de Website.
8.2 Onze Responstijden staan op de Website of in de met u overeengekomen service level overeenkomst. Het kan zijn dat u kortere Responstijden wenst. Als u een dergelijke behoefte heeft, kunt u dit aan ons kenbaar maken. Indien mogelijk kunnen wij u dan een aanbod doen voor kortere reactietijden. Dit aanbod zal afhankelijk zijn van uw bereidheid om een extra vergoeding aan ons te betalen.
8.3 Wanneer u een Incident meldt, dient u ons te voorzien van de informatie die wij redelijkerwijs nodig hebben om de fout in het Platform of de Software die het Incident veroorzaakt te kunnen repliceren.
8.4 Wij kunnen ervoor kiezen een work-around te bieden om een Incident op te lossen als het oplossen van de fout die het Incident heeft veroorzaakt waarschijnlijk een negatieve impact zal hebben op de Functionaliteit of uw gebruik van de Software, zoals voor u van toepassing.
8.5 Als wij van mening zijn dat een gemeld Incident is veroorzaakt door gebruik van de Cloud Dienst of de Software in strijd met de Documentatie of met deze AV, zullen wij dit aan u melden. Een dergelijk Incident wordt niet gedekt door Ondersteuning. Als u dan nog steeds wilt dat wij het Incident oplossen, kunnen wij u hiervoor een vergoeding per uur tegen onze dan geldende tarieven in rekening brengen.
8.6 Wanneer uw Gebruikers een onevenredig groot aantal supportoproepen bij ons indienen of een bovengemiddeld aantal Incidenten veroorzaken, kunnen wij eisen dat u voor deze Gebruikers Training bij ons afneemt. Als u dit niet doet, kunnen wij onze Support-verplichtingen opschorten.
9. Verplichtingen Klant
9.1 Wanneer u gebruik maakt van de Clouddienst of de Software moet u de installatie- en softwarecompatibiliteitsrichtlijnen in acht nemen die door ons in de Documentatie worden verstrekt. Als u deze richtlijnen niet in acht neemt, kunt u mogelijk geen gebruik maken van de Clouddienst of de Software en komt u niet in aanmerking voor Ondersteuning, afhankelijk van wat u hebt gekozen om te gebruiken.
9.2 U bent verantwoordelijk voor het onderhouden van een werkende internetverbinding met het Platform.
10. Intellectuele eigendomsrechten
10.1 Wij garanderen dat wij alle benodigde rechten hebben voor het leveren van de Cloud Dienst, inclusief, als voor u van toepassing, alle benodigde rechten voor het leveren van een licentie om de Software te gebruiken.
10.2 De Intellectuele Eigendomsrechten in het Platform en de Software blijven bij ons of bij onze leveranciers, u krijgt alleen een recht op toegang tot het Platform en het daaropvolgende gebruik van de Functionaliteit of, indien van toepassing voor u, gebruik van de Software, zoals beschreven in de Overeenkomst of anderszins schriftelijk overeengekomen.
10.3 Het is u niet toegestaan enige aanduiding betreffende een Intellectueel Eigendomsrecht uit het Platform en/of de Software te verwijderen of te wijzigen, met inbegrip van aanduidingen betreffende het vertrouwelijke karakter en geheimhouding van informatie in het Platform en/of de Software.
10.4 Het is ons toegestaan om technische maatregelen te nemen ter beveiliging van de Cloud Dienst en/of de Software. Indien wij dit hebben gedaan mag u deze beveiliging niet verwijderen of omzeilen. Technische maatregelen zullen u niet verbieden om dwingende wettelijke gebruiksrechten met betrekking tot de Clouddienst en de Software uit te oefenen.
10.5 Wij mogen de inzichten en andere kennis die wij en ons personeel door onze uitvoering van de Overeenkomst verwerven, vrij gebruiken, op voorwaarde dat dit gebruik geen inbreuk vormt op uw eigendomsrechten.
10.6 Het is u niet toegestaan domeinen of social mediakanalen te gebruiken die de naam AttachingIT en/of Smartlockr bevatten zonder vooraf onze toestemming te hebben gevraagd.
11. Opleiding
11.1 Onze docenten die een Training verzorgen hebben voldoende kennis van de Functionaliteit en beschikken over de didactische vaardigheden die nodig zijn om de Training naar behoren te verzorgen.
11.2 Wij verstrekken elke deelnemer opleidingsmateriaal voor eigen persoonlijk gebruik. Deelnemers mogen het opleidingsmateriaal alleen reproduceren voor persoonlijke naslagdoeleinden.
11.3 U kunt een Training kosteloos annuleren tot vijf dagen voor de geplande Trainingsdatum. Als u annuleert binnen vijf dagen voor de geplande Trainingsdatum mogen wij de kosten voor de Training aan u doorbelasten
12. Prijzen, tarieven, facturering en betaling
12.1 Alle overeengekomen prijzen en tarieven en het gelicentieerde aantal Gebruikers staan vermeld in het Geaccepteerde Voorstel. Alle vermelde prijzen en tarieven zijn exclusief btw.
12.2 Wij mogen de overeengekomen prijzen en tarieven jaarlijks met ingang van 1 januari verhogen. Wij zullen u uiterlijk 31 oktober van het voorafgaande jaar op de hoogte stellen van een voorgenomen prijsverhoging. Als u het niet eens bent met de voorgenomen prijsverhoging, is de enige remedie die u ter beschikking staat een kosteloze beëindiging van de Overeenkomst.
12.3 Prijswijzigingen ten gevolge van inflatie of die verband houden met substantiële Functionaliteitsverbeteringen kunnen rechtstreeks in rekening worden gebracht. U heeft bij deze prijswijzigingen geen recht op kosteloze beëindiging van de Overeenkomst.
12.4 Wij sturen een factuur voor de eenmalige kosten en de terugkerende jaarlijkse kosten voor de volledige Looptijd op de datum van ondertekening van de Overeenkomst. Eventuele terugkerende vergoedingen die verschuldigd zijn na een verlenging van de Overeenkomst worden jaarlijks vooraf gefactureerd.
12.5 Als specifieke diensten en werkzaamheden niet onder de Overeenkomst vallen, dan kunnen wij u een factuur sturen voor de werkelijk gewerkte uren tegen de dan geldende uurtarieven. Als wij worden gevraagd aanvullende diensten te verrichten, zullen wij u een offerte voor die diensten doen toekomen. Pas na ontvangst van de goedkeuring van dit voorstel, zullen wij deze aanvullende diensten verrichten. Voor meerwerk dat redelijkerwijs noodzakelijk is of voortvloeit uit uw voorafgaande instructies, is geen voorafgaande goedkeuring nodig. Wanneer in een offerte of werkomschrijving een vaste prijs is vermeld, wordt meerwerk niet in rekening gebracht, tenzij het buiten de werkomschrijving valt en vooraf goedkeuring is verleend.
12.6 Extra functionaliteiten die aan u worden verstrekt gedurende de Looptijd, zullen pro rata worden gefactureerd tot de volgende terugkerende factuurdatum.
12.7 U dient alle verschuldigde bedragen binnen 14 (veertien) dagen na de factuurdatum aan ons te betalen.
12.8 Als u de factu(u)r(en) betwist, doet deze betwisting geen afbreuk aan uw verplichting om het onbetwiste gedeelte van de factu(u)r(en) te betalen.
12.9 Als u de gefactureerde bedragen niet binnen de betalingstermijn betaalt, bent u over het openstaande bedrag de wettelijke rente verschuldigd zonder dat enige voorafgaande ingebrekestelling nodig is, tenzij u de factuur binnen 10 (tien) dagen na factuurdatum heeft betwist. Als u met betaling van de factuur in gebreke blijft, kunnen wij naast de wettelijke rente aanspraak maken op vergoeding van buitengerechtelijke incassokosten tegen een percentage van tenminste 15% van het totale factuurbedrag.
12.10 Als u achterstallig bent met de betaling van twee opeenvolgende facturen, kunnen wij uw toegang tot het Platform opschorten, op voorwaarde dat wij u schriftelijk (inclusief e-mail) op de hoogte hebben gesteld van ons voornemen daartoe en u ten minste 5 (vijf) Werkdagen de tijd hebt gekregen om volledig aan uw betalingsverplichtingen te voldoen, d.w.z. inclusief wettelijke rente, buitengerechtelijke en andere kosten.
13. Duur, beëindiging, verlenging en uittreding
13.1 De Overeenkomst treedt in werking op de Ingangsdatum.
13.2 De Overeenkomst wordt gesloten voor een initiële duur van minimaal één (1) jaar, tenzij anders wordt overeengekomen.
13.3 De Overeenkomst wordt – ongeacht de looptijd – steeds automatisch verlengd met de initieel overeengekomen duur, tenzij noch u noch wij de Overeenkomst uiterlijk drie (3) maanden voor de verlengingsdatum per aangetekende brief met ontvangstbevestiging hebben opgezegd.
13.4 U en wij mogen:
a. De Overeenkomst met onmiddellijke ingang schriftelijk (met inbegrip van e-mail) beëindigen indien de andere partij haar verplichtingen uit hoofde van de Overeenkomst niet nakomt en deze nalatigheid voortduurt na kennisgeving aan de andere partij waarbij deze een redelijke termijn wordt gegeven om alsnog aan haar verplichtingen te voldoen.
b. Zonder nadere ingebrekestelling de Overeenkomst door middel van een aangetekend schrijven met onmiddellijke ingang beëindigen indien de andere partij surséance van betaling aanvraagt of deze wordt verleend; de andere partij faillissement aanvraagt of wordt uitgesproken; de onderneming van de andere partij wordt geliquideerd of beëindigd anders dan ten behoeve van een fusie; er beslag wordt gelegd op een substantieel deel van de activa van de andere partij of de infrastructuur en/of de computerprogrammatuur in verband met de uitvoering van de Overeenkomst, of de andere partij niet langer geacht kan worden de verplichtingen uit de Overeenkomst na te komen.
13.5 Als de Overeenkomst door u wordt beëindigd op grond van artikel 13.4, heeft u het recht om het gebruik van de Functionaliteit of, indien voor u van toepassing, de Software, gedurende twee (2) opeenvolgende maanden voort te zetten tegen een redelijke, door ons vast te stellen en door u vooruit te betalen vergoeding.
13.6 Behalve voor zover bepaald in artikel 13.5, vervallen al uw rechten bij beëindiging van de Overeenkomst.
13.7 Tenzij anders bepaald, blijven de verplichtingen die naar hun aard bestemd zijn om ook na de beëindiging van de Overeenkomst voort te duren, ook na de beëindiging ervan gelden. De bepalingen over vertrouwelijkheid, aansprakelijkheid, intellectuele eigendomsrechten, toepasselijk recht en bevoegdheid gelden ook de beëindiging van de Overeenkomst.
14. Prestaties
14.1 Wij zullen de Diensten met zorg en naar beste vermogen uitvoeren en in overeenstemming met de Overeenkomst. Onze verplichting om aan u de Diensten te leveren, is een inspanningsverbintenis, tenzij en voor zover wij in de Overeenkomst uitdrukkelijk een bepaald resultaat hebben toegezegd en het resultaat met voldoende bepaaldheid is omschreven.
14.2 Zowel het Platform als de Software zullen overwegend functioneren in overeenstemming met de Documentatie.
15. Aansprakelijkheid
15.1 Onze totale aansprakelijkheid voor onze toerekenbare tekortkoming in de nakoming van de Overeenkomst is beperkt tot onze vergoeding van uw daaruit voortvloeiende directe financiële schade tot maximaal de vergoedingen (exclusief btw en andere overheidsheffingen) die wij van u hebben ontvangen in de twaalf (12) maanden, direct voorafgaand aan de maand waarin het schade brengende feit zich heeft voorgedaan. Directe vermogensschade bestaat uitsluitend uit:
a. Redelijke kosten die u zou moeten maken om ervoor te zorgen dat wij niet in strijd met de Overeenkomst zouden handelen; deze kosten worden echter niet vergoed indien de Overeenkomst door u of namens u wordt ontbonden.
b. Redelijke kosten gemaakt door u voor het moeten voortzetten van de oplossing die u gebruikte om uzelf te voorzien van de Functionaliteit voor uw voorgenomen gebruik van het Platform of de Software.
c. Redelijke kosten, gemaakt ter vaststelling van de oorzaak en de omvang van de schade, voor zover de vaststelling betrekking heeft op directe vermogensschade in de zin van deze voorwaarden.
d. Redelijke kosten, gemaakt ter voorkoming of beperking van schade, voor zover u kunt aantonen dat deze kosten hebben geleid tot beperking van directe schade in de zin van deze voorwaarden.
15.2 Aansprakelijkheid voor andere dan de in artikel 15.1 genoemde schade, met inbegrip van, maar niet beperkt tot gevolgschade, gederfde winst, gemiste besparingen, verlies van gegevens en schade door bedrijfsstagnatie, wordt uitdrukkelijk uitgesloten.
15.3 De voornoemde beperkingen van aansprakelijkheid zijn niet van toepassing:
a. Indien er een vordering tot schadevergoeding is die gevolgd wordt door overlijden of lichamelijk letsel;
b. Indien de schade het rechtstreekse gevolg is van onze grove nalatigheid of opzettelijke opzet.
15.4 Schade als bedoeld in artikel 15.1 dient zo spoedig mogelijk, doch uiterlijk binnen twee (2) weken na het ontstaan daarvan, schriftelijk of per e-mail aan ons te worden gemeld. Schade die niet binnen deze termijn ter kennis van ons is gebracht, kunt u niet verhalen.
16. Overmacht
16.1 Als wij door overmacht tekortschieten in de nakoming van enige verplichting uit de Overeenkomst, kunt u, na verloop van een termijn van tenminste dertig (30) dagen, de Overeenkomst door middel van een aangetekende brief ontbinden. Als u dit doet bent u ons geen vergoeding verschuldigd. Voor de door ons tot aan de datum van beëindiging verrichte Diensten, waarvoor de vergoeding nog niet aan u is gefactureerd, kunnen wij u een factuur sturen die u overeenkomstig deze AV zult voldoen.
16.2 Wij kunnen ons in ieder geval op overmacht beroepen indien een van de volgende omstandigheden zich heeft voorgedaan: niet-toerekenbare tekortkoming van toeleveranciers, verlies van gegevens, stroomstoringen, storingen in de telecommunicatie-infrastructuur, licentieweigeringen, (distributed) denial of service attacks en/of uitval van netwerkverbindingen.
17. Vertrouwelijkheid
17.1 Zonder uw uitdrukkelijke voorafgaande schriftelijke toestemming zullen wij aan derden geen bestanden ter beschikking stellen die door middel van het Platform worden verwerkt, met inbegrip van de gegevens van de afzender en de ontvanger van het bestand (gezamenlijk "Vertrouwelijke Informatie"). Vertrouwelijke Informatie zal alleen ter beschikking worden gesteld aan onze medewerkers op een strikte "need to know" basis en in de mate dat een dergelijke beschikbaarheid vereist is om de overeengekomen Dienst te kunnen uitvoeren. Wij kunnen Vertrouwelijke Informatie bekendmaken indien wij daartoe wettelijk verplicht zijn. Indien wettelijk mogelijk zullen wij u vooraf op de hoogte stellen van een dergelijke openbaarmaking, zodat u in staat bent om hiertegen bezwaar te maken.
18.Bescherming van persoonsgegevens
18.1 Wij zullen persoonlijke gegevens op het Platform verwerken in overeenstemming met onze privacyverklaring en de Toepasselijke Wetgeving inzake Gegevensbescherming. Als wij persoonsgegevens verwerken in onze rol als uw verwerker, doen wij dat in overeenstemming met de voorwaarden in Annex 2 (verwerkersovereenkomst). Bij een intern conflict gaat de inhoud van Annex 2 voor op de inhoud van deze AV (inclusief Annex 1).
19. Overdracht van rechten en verplichtingen
19.1 U mag uw rechten en verplichtingen uit deze Overeenkomst niet overdragen aan derden zonder onze schriftelijke toestemming.
19.2 Wij kunnen te allen tijde de rechten en verplichtingen die voortvloeien uit de Overeenkomst overdragen.
19.3 Bij de uitvoering van de Overeenkomst kunnen wij gebruik maken van de diensten van derden, hetzij als onderaannemer, hetzij door tijdelijke inhuur van personeel. Ons recht laat onverlet onze verantwoordelijkheid voor de nakoming van onze verplichtingen uit hoofde van de Overeenkomst.
20. Toepasselijk recht en geschillenbeslechting
20.1 De Overeenkomst wordt beheerst door Nederlands recht.
20.2 Alle geschillen die mochten ontstaan naar aanleiding van of in verband met de Overeenkomst zullen worden voorgelegd aan de bevoegde rechter te Amsterdam.
21. Diversen
21.1 Mondelinge verklaringen, toezeggingen of afspraken in verband met de uitvoering van de Overeenkomst hebben geen rechtskracht, tenzij zij schriftelijk zijn bevestigd door de partij die ze heeft gedaan.
21.2 Het verzuim van een partij om binnen een in de Overeenkomst gestelde termijn nakoming van enige bepaling te verlangen, tast het recht om alsnog nakoming te verlangen niet aan, tenzij de partij uitdrukkelijk schriftelijk met deze niet-nakoming heeft ingestemd.
21.3 Indien een bepaling van de Overeenkomst nietig of niet-afdwingbaar is, blijven de overige bepalingen van deze Overeenkomst van kracht en overleggen de partijen om een vervangende bepaling overeen te komen die de ongeldige (vernietigde/vernietigde) bepaling zoveel mogelijk benadert binnen het toepassingsgebied van de Overeenkomst.
Annex 1 - AUP
(1) Dit beleid
Dit Beleid voor Aanvaardbaar Gebruik (het "Beleid") beschrijft de regels voor het gebruik van de Clouddienst en alle inhoud die u naar de Clouddienst kunt sturen ("Inhoud").
(2) Algemene beperkingen
U mag de Dienst niet gebruiken op een manier die schade aan de Clouddienst veroorzaakt, of kan veroorzaken, of die de beschikbaarheid of toegankelijkheid van de Clouddienst, of een van de gebieden van, of diensten op, de Clouddienst aantast.
U mag de Clouddienst niet gebruiken:
a. Op een wijze die onwettig, frauduleus of schadelijk is; of
b. In verband met enig onwettig, frauduleus of schadelijk doel of activiteit.
(3) Licentie
U verleent ons een wereldwijde, onherroepelijke, niet-exclusieve, royalty-vrije licentie om uw Inhoud te gebruiken, te reproduceren en te distribueren voor zover wij deze rechten nodig hebben om u van de Clouddienst te kunnen voorzien.
(4) Onwettige inhoud
U mag de Clouddienst niet gebruiken om Inhoud op te slaan, te hosten, te kopiëren, te distribueren, weer te geven, te publiceren of te verzenden die onwettig is, of die inbreuk maakt of kan maken op de wettelijke rechten van een derde, of die aanleiding kan geven tot gerechtelijke stappen tegen u of ons of een derde (in elk geval in elk rechtsgebied en onder elke toepasselijke wet).
Inhoud mag niet:
a. Inbreuk maken op auteursrechten, morele rechten, databankrechten, handelsmerkrechten, modelrechten, rechten op het doorgeven van namaak, of andere intellectuele eigendomsrechten;
b. Inbreuk maken op vertrouwelijkheidsrechten, privacy rechten of rechten uit hoofde van de wetgeving inzake gegevensbescherming;
c. In strijd zijn met de officiële geheimhoudingswetgeving;
d. In strijd zijn met een contractuele verplichting naar een derde.
e. Het voorwerp hebben uitmaakt of ooit hebben uitgemaakt van een dreigende of daadwerkelijke rechtszaak of andere gelijkaardige klacht.
(5) Schadelijke software
U mag de Cloud Dienst niet gebruiken om virussen, Trojaanse paarden, wormen, rootkits, spyware, [adware] of andere schadelijke software, programma's, routines, applicaties of technologieën te promoten of te verspreiden.
U mag de Clouddienst niet gebruiken om software, programma's, routines, applicaties of technologieën te promoten of te verspreiden die de prestaties van een computer negatief (kunnen) beïnvloeden of aanzienlijke veiligheidsrisico's voor een computer introduceren.
(6) Marketing en spam
U mag de Clouddienst niet gebruiken voor doeleinden die verband houden met marketing, reclame, promotie, of de levering en/of verkoop van goederen en/of diensten.
De inhoud mag geen spam zijn.
U mag de Clouddienst niet gebruiken om ongevraagde commerciële berichten te versturen.
U mag de Cloud Dienst niet gebruiken om kettingbrieven, ponzi-schema's, piramideschema's, matrixprogramma's, "word snel rijk"-schema's of gelijksoortige schema's, programma's of materialen op de markt te brengen, te verspreiden of te posten.
(7) Inbreuken op dit beleid
Als u dit Beleid op enigerlei wijze schendt, of als wij redelijkerwijs vermoeden dat u dit Beleid op enigerlei wijze hebt geschonden, kunnen wij:
a. Uw Inhoud te verwijderen of te bewerken;
b. U een of meer formele waarschuwingen sturen;
c. Uw toegang tot een deel van of de gehele Clouddienst tijdelijk op te schorten; en/of
d. U permanent verbieden om een deel of de hele Clouddienst te gebruiken.
De uitoefening van deze rechten doet geen afbreuk aan onze andere rechten uit hoofde van de Overeenkomst.
(8) Verbannen gebruikers
Wanneer wij uw toegang tot de Clouddienst of een deel van de Clouddienst opschorten of verbieden, mag u geen actie ondernemen om een dergelijke opschorting of verbod te omzeilen (inclusief maar niet beperkt tot het gebruik van een ander account).
(9) Toezicht
Niettegenstaande de bepalingen van dit Beleid, controleren wij de Inhoud niet actief.
Annex 2 – VERWERKERSOVEREENKOMST
OVERWEGINGEN
a. Wij op grond van de Overeenkomst aan u de middelen bieden om op een beveiligde manier berichten en bestanden te versturen en te ontvangen;
b. Het ontwerp van deze middelen erop gericht is dat wij geen kennis kunnen nemen van de inhoud van berichten en aangehechte bestanden, maar dat zich daarin desondanks persoonsgegevens bevinden in de zin van de Algemene Verordening Gegevensbescherming (“AVG”); en
c. Wij daarom schriftelijke afspraken met u maken over het mogelijke verwerken van dergelijke persoonsgegevens (hierna de “Verwerkersovereenkomst”). De persoonsgegevens die wij mogelijk verwerken en de categorieën betrokkenen die het betreft, zijn beschreven in een overzicht dat wij publiceren op onze Website. U kunt dit overzicht hier raadplegen.
KOMEN WIJ HET VOLGENDE OVEREEN:
1. Definities
1.1 Alle in deze Verwerkersovereenkomst aangeduide begrippen moeten worden geïnterpreteerd overeenkomstig:
a. Artikel 4 van Verordening 2016/679 van het Europees Parlement en de Raad van 27 april 2016 betreffende de bescherming van natuurlijke personen in verband met de verwerking van persoonsgegevens en betreffende het vrije verkeer van die gegevens en tot intrekking van Richtlijn 95/46/EG (hierna “AVG”); en
b. De inhoud van het Geaccepteerde Voorstel en artikel 1 van de AV.
1.2 Een verwijzing naar een specifieke norm (zoals ISO en Nen-normen) is een verwijzing naar de meest actuele versie van die norm. Indien de betreffende norm niet meer wordt onderhouden, dient in de plaats daarvan de meest actuele versie van de logische opvolger van de betreffende norm gelezen te worden.
2. Onderwerp van deze Verwerkersovereenkomst
2.1 Deze Verwerkersovereenkomst is van toepassing op het verwerken van Persoonsgegevens die zich bevinden in berichten en bestanden die uw Gebruikers versturen en ontvangen met behulp van de onder de Overeenkomst aangeboden technische middelen.
2.2. Wanneer informatie die uw Gebruikers door middel van de aangeboden middelen versturen of ontvangen Persoonsgegevens bevatten dan verwerken wij deze in de hoedanigheid van Verwerker namens u als Verantwoordelijke in de zin van de AVG.
3. Duur en beëindiging
3.1 Deze Verwerkersovereenkomst maakt integraal en onlosmakelijk deel uit van de Overeenkomst.
3.2 Deze Verwerkersovereenkomst gaat in op het moment van totstandkoming van de Overeenkomst. Beëindiging van de Overeenkomst leidt eveneens tot beëindiging van deze Verwerkersovereenkomst.
3.3 De relevante verplichtingen uit deze Verwerkersovereenkomst blijven na het beëindigen van de Overeenkomst van kracht totdat alle Persoonsgegevens die op grond daarvan nog worden verwerkt zijn vernietigd of verwijderd.
4. Uitvoering verwerking
4.1 Wij verwerken Persoonsgegevens die wij op grond van Artikel 2 onder ons houden uitsluitend in opdracht van u en voor zover dit noodzakelijk is ter uitvoering van de Overeenkomst of schriftelijk met u gemaakte afspraken.
4.2 Een wezenlijk kenmerk van de technische middelen die wij leveren, is dat deze zijn ontworpen om te voorkomen dat wij kennis kunnen nemen van de inhoud van berichten en bestanden die daarmee worden verwerkt. Onze faciliteiten stellen u daarom in staat om alle inhoudelijke handelingen ten aanzien van Persoonsgegevens die nodig zijn om aan uw verplichtingen uit hoofde van de AVG te voldoen zelf te verrichten.
4.3 In zover de aard van de faciliteiten die wij leveren dit toestaat, zullen wij;
a. Alle door U op grond van deze Verwerkersovereenkomst gegeven redelijke en rechtmatige instructies ten aanzien van het verwerken van Persoonsgegevens uitvoeren; en
b. Alle redelijkerwijs door u gevraagde informatie en ondersteuning bieden om u in staat te stellen te voldoen aan uw verplichtingen uit hoofde van de AVG.
Wij zullen u informeren indien het voldoen aan dergelijke instructies of verzoeken in strijd is met een op ons rustende wettelijke verplichting. In geen geval verplicht deze wettelijke bepaling ons tot aanpassing van de door ons geleverde technische middelen.
4.4 Wij mogen bij een vergoeding in rekening brengen in lijn met artikel 12.5 van de AV voor ondersteuning die wij bieden op grond van deze Verwerkersovereenkomst. Daaronder vallen in het bijzonder werkzaamheden op basis van het uitgangspunt van artikel 4.3 en werkzaamheden ter ondersteuning van een onderzoek op grond van artikel 7.2.
4.5 Onverminderd het bepaalde in artikel 4.1 mogen wij Persoonsgegevens verwerken indien wij dat moeten doen op grond van de wet. Wij zullen u in dat geval voorafgaand aan de verwerking schriftelijk melden dat wij dat gaan doen, tenzij die melding wettelijk verboden is.
5. Geheimhouding
5.1 Wij behandelen Persoonsgegevens als strikt vertrouwelijk en dragen er zorg voor dat deze niet ter beschikking komen van derden, tenzij dit noodzakelijk is voor de uitvoerig van verplichtingen uit hoofde van de Overeenkomst of de wet ons verplicht om die verstrekking te doen.
5.2 Onze werknemers, vertegenwoordigers en/of derden die namens ons betrokken zijn bij het verwerken van Persoonsgegevens zijn contractueel verplicht Persoonsgegevens die zij verwerken, geheim te houden.
6. Beveiliging
6.1 Wij nemen en onderhouden passende technische en organisatorische beveiligingsmaatregelen om Persoonsgegevens in het licht van de stand van de techniek en de daarmee gemoeide kosten adequaat te beschermen tegen verlies, onbevoegde kennisname, verminking of enige andere vorm van onrechtmatige verwerking.
6.2 Wij onderhouden ons beveiligingsbeleid voor de bescherming van Persoonsgegevens in overeenstemming met ISO27001:2017, NEN7510:2018 en NEN: NTA 7516. In het verlengde hiervan onderhouden wij ten minste de volgende beveiligingsmaatregelen:
a. Maatregelen om te waarborgen dat enkel bevoegde personen toegang hebben tot de Persoonsgegevens en wel voor de doeleinden die zijn uiteengezet;
b. Maatregelen waarbij wij medewerkers en derden uitsluitend via op naam gestelde accounts en voor noodzakelijke doeleinden toegang verschaffen tot systemen waarop Persoonsgegevens worden verwerkt, waarbij het gebruik van die accounts adequaat gelogd wordt;
c. Maatregelen om de Persoonsgegevens te beschermen tegen onopzettelijke of onrechtmatige vernietiging, onopzettelijk verlies of wijziging, onbevoegde of onrechtmatige opslag, verwerking, toegang of openbaarmaking;
d. Maatregelen om zwakke plekken te identificeren ten aanzien van de verwerking van Persoonsgegevens in de systemen die worden ingezet voor het verlenen van diensten aan uw organisatie;
e. Maatregelen om de tijdige beschikbaarheid van de Persoonsgegevens te garanderen;
f. Maatregelen om te waarborgen dat Persoonsgegevens logisch gescheiden worden verwerkt van de Persoonsgegevens die wij voor onze eigen organisatie of namens derden verwerken.
7. Monitoring en audits
7.2 Wij stellen u eenmaal per jaar in staat om een onafhankelijke derde onderzoek te laten doen naar Onze naleving van deze Verwerkersovereenkomst in zoverre een certificaat of rapport als bedoeld in artikel 7.1 U redelijkerwijs niet in staat stelt om te voldoen aan uw toezichtverplichtingen op grond van de AVG. De beperking tot een jaarlijkse controle geldt niet als objectieve gronden een vermoeden rechtvaardigen dat wij niet voldoen aan onze verplichtingen uit hoofde van deze Verwerkersovereenkomst.
7.3 U moet een onderzoek op grond van artikel 7.2 tenminste 30 kalenderdagen voorafgaand aan de beoogde uitvoering daarvan aankondigen. Het onderzoek moet worden uitgevoerd tijdens normale kantooruren door een onafhankelijk en erkend extern accountantskantoor dat schriftelijk gehouden is tot geheimhouding. Als het onderzoek aantoont dat wij op materiele wijze tekortschieten in de nakoming van deze Verwerkersovereenkomst dan zullen wij onverwijld een mitigatieplan opstellen uitvoeren.
7.4 U bent verantwoordelijk voor alle kosten verbonden aan onderzoek op grond van artikel 7.2, tenzij het onderzoek aantoont dat wij op materiele wijze tekortschieten in de nakoming van onze verplichtingen uit deze Verwerkersovereenkomst.
8. Management van Inbreuken
8.1 Indien zich bij ons of bij een door of namens ons ingeschakelde derde een Inbreuk In Verband Met Persoonsgegevens (een “Inbreuk”) voordoet, of een redelijk vermoeden bestaat dat dit zich voordoet of heeft voorgedaan dan informeren wij u daarover onverwijld. Wij zullen daarover alle redelijkerwijs relevante informatie verstrekken waaronder:
1) De aard van de Inbreuk en/of de situatie;
2) De geconstateerde en de vermoedelijke gevolgen van de Inbreuk; en
3) De maatregelen die getroffen zijn, of door Ons beoogd worden, om de Inbreuk op te lossen en om de potentiële gevolgen/schade daarvan zoveel mogelijk te beperken.
8.2 Onverminderd de overige verplichtingen uit deze Verwerkersovereenkomst zijn wij gehouden, en vrijwaart U Ons ertoe, om alle maatregelen te treffen die redelijkerwijs van ons kunnen worden verwacht om een Inbreuk te onderzoeken, daarvan te herstellen en om verdere gevolgen daarvan te beperken.
9. Inschakeling van derden
9.1 Wij kunnen in het kader van de uitvoering van deze Verwerkersovereenkomst genoodzaakt zijn om derden in te schakelen (“Subverwerkers”). Wij leggen Subverwerkers tenminste dezelfde verplichtingen op als waaraan wij op grond van deze Verwerkersovereenkomst gebonden zijn. Wij leggen deze afspraken schriftelijk vast en zien erop toe dat deze worden nageleefd. Wij blijven verantwoordelijk voor de eventuele gevolgen van het door ons uitbesteden van de Verwerking van Persoonsgegevens aan derden.
9.2 Wij publiceren alle relevante informatie over onze Subverwerkers op onze website. U stemt met het aangaan van de Hoofdovereenkomst in met het gebruik van de Subverwerkers die al aangesteld zijn. Als wij het voornemen hebben om een nieuwe Subverwerker aan te stellen dan zullen wij U daarvan tenminste 3 maanden van tevoren elektronisch in kennis stellen en u om toestemming vragen wanneer dit uit hoofde van de AVG vereist is.
9.3 Als u naar aanleiding van een kennisgeving op grond artikel 9.1 niet instemt met het voornemen dan heeft u het recht om de Hoofdovereenkomst binnen 60 kalenderdagen na ontvangst van deze kennisgeving schriftelijk te beëindigen. Indien u van dit recht geen gebruik maakt dan wordt u geacht met het voornemen in te stemmen.
10. Internationale gegevensoverdracht
10.1 Wij verwerken geen Persoonsgegevens, en laten derden geen Persoonsgegevens verwerken, in landen of gebieden buiten de Europese Economische Ruimte, tenzij:
a. De Europese Commissie ten aanzien daarvan heeft besloten dat deze een passend niveau van bescherming waarborgen voor Persoonsgegevens;
b. U daartoe op ons verzoek schriftelijk uw toestemming heeft gegeven; of
c. Voldaan wordt aan een van de andere gronden die de AVG daartoe biedt.
11. Bewaartermijnen, teruggave en vernietiging van Persoonsgegevens
11.1. Wij bewaren Persoonsgegevens die wij op grond van deze Verwerkersovereenkomst onder ons hebben niet langer dan strikt noodzakelijk is voor het verlenen van onze diensten onder de Hoofdovereenkomst en het nakomen van eventuele wettelijke bewaarplichten.
11.2. De aard van de middelen brengt mee dat wij geen toegang hebben tot Persoonsgegevens die wij ter uitvoering van deze Verwerkersovereenkomst onder Ons hebben. U bent ertoe gehouden dat u alle Persoonsgegevens die wij onder deze Verwerkersovereenkomst verwerken, kopieert of migreert en veiligstelt alvorens u de Overeenkomst beëindigt.
11.3. Wij vernietigen de Persoonsgegevens na beëindiging van de Overeenkomst en het verstrijken van geldende bewaartermijnen onverwijld en onherroepelijk, tenzij u voorafgaand aan deze beëindiging afspraken met ons maakt over aanvullende bewaartermijnen.
11.4. Op Uw verzoek verstrekken wij u een verklaring van het feit dat de Persoonsgegevens onherroepelijk zijn vernietigd of verwijderd. Indien onherroepelijke vernietiging of verwijdering niet mogelijk is dan stellen wij u daarvan onverwijld op de hoogte. De Persoonsgegevens worden in voorkomende gevallen vertrouwelijk behandeld tot aan het moment dat zij alsnog zijn vernietigd of verwijderd.